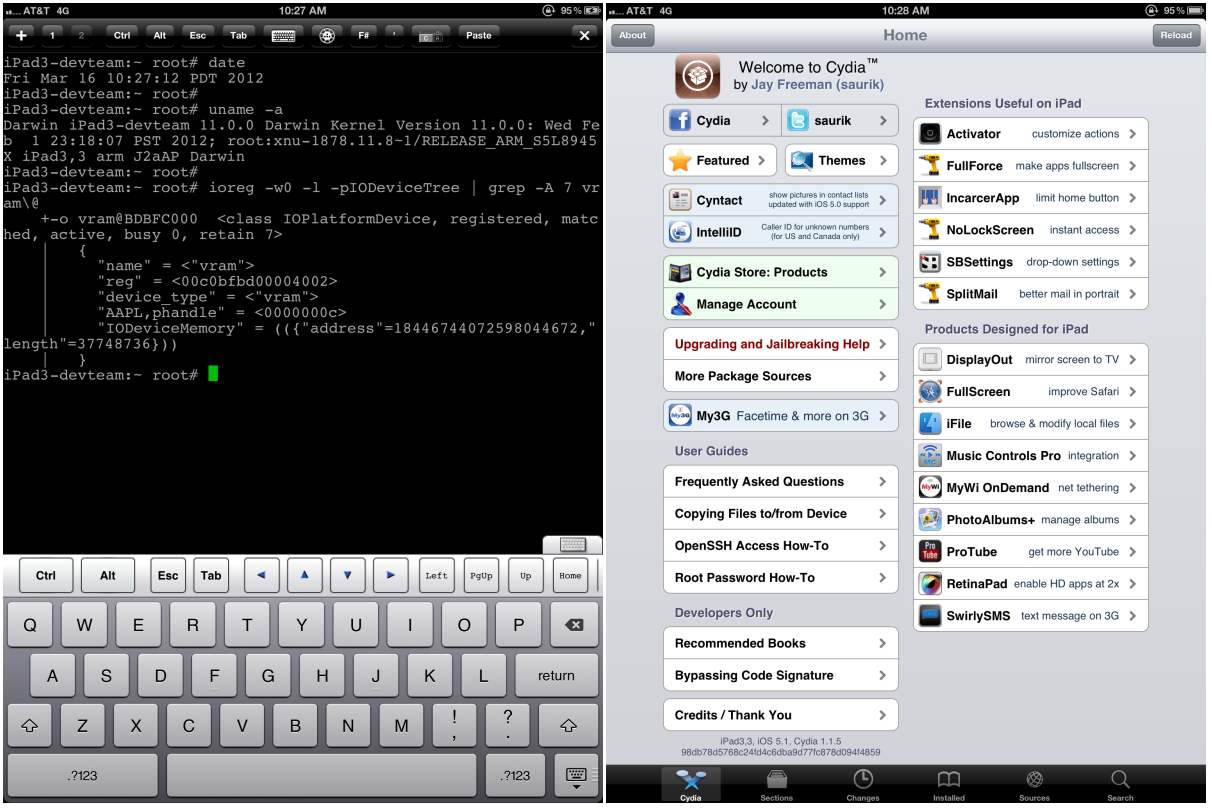
evasi0n Jailbreakers reveal the incredibly complicated methods they used to Jailbreak every Apple iOS device
 Forbes posted an article on Tuesday that gave some updates on the highly successful launch of the evasi0n jailbreak tool straight from its creators. After having officially released the jailbreak yesterday at noon, according to stats from Cydia’s Jay Freeman, around 1.7 million people have decided to jailbreak their iOS device. Perhaps more interesting is a description of how exactly the four members of the evad3rds team were able to get the job done. Team member David Wang, aka @planetbeing, walked through the process with Forbes:
Forbes posted an article on Tuesday that gave some updates on the highly successful launch of the evasi0n jailbreak tool straight from its creators. After having officially released the jailbreak yesterday at noon, according to stats from Cydia’s Jay Freeman, around 1.7 million people have decided to jailbreak their iOS device. Perhaps more interesting is a description of how exactly the four members of the evad3rds team were able to get the job done. Team member David Wang, aka @planetbeing, walked through the process with Forbes:
Evasi0n alters the socket that allows programs to communicate with a program called Launch Daemon, abbreviated launchd, a master process that loads first whenever an iOS device boots up and can launch applications that require “root” privileges, a step beyond the control of the OS than users are granted by default. That means that whenever an iPhone or iPad’s mobile backup runs, it automatically grants all programs access to the time zone file and, thanks to the symbolic link trick, access to launchd.
Wang described the entire process from finding the initial exploit in the iOS mobile backup system to accessing Launch Daemon and getting around code signing and restrictions at the kernel layer:
Once it’s beaten ASLR, the jailbreak uses one final bug in iOS’s USB interface that passes an address in the kernel’s memory to a program and “naively expects the user to pass it back unmolested,” according to Wang. That allows evasi0n to write to any part of the kernel it wants. The first place it writes is to the part of the kernel that restricts changes to its code–the hacker equivalent of wishing for more wishes. ”Once you get into the kernel, no security matters any more,” says Wang. “Then we win.”
Go to Forbes to read Wang’s entire step-by-step description of the jailbreak process for evasi0n.
Here’s another third-party analysis. The verdict is the same: incredible work.