A company selling password-cracking tools says that a newly-discovered T2 Mac security vulnerability allows it to crack passwords on these machines, bypassing the lockouts.
The method used is far slower than conventional password-cracking tools, but although the total time needed could run into thousands of years, that could fall to as little as 10 hours when the Mac owner has used a more typical password…
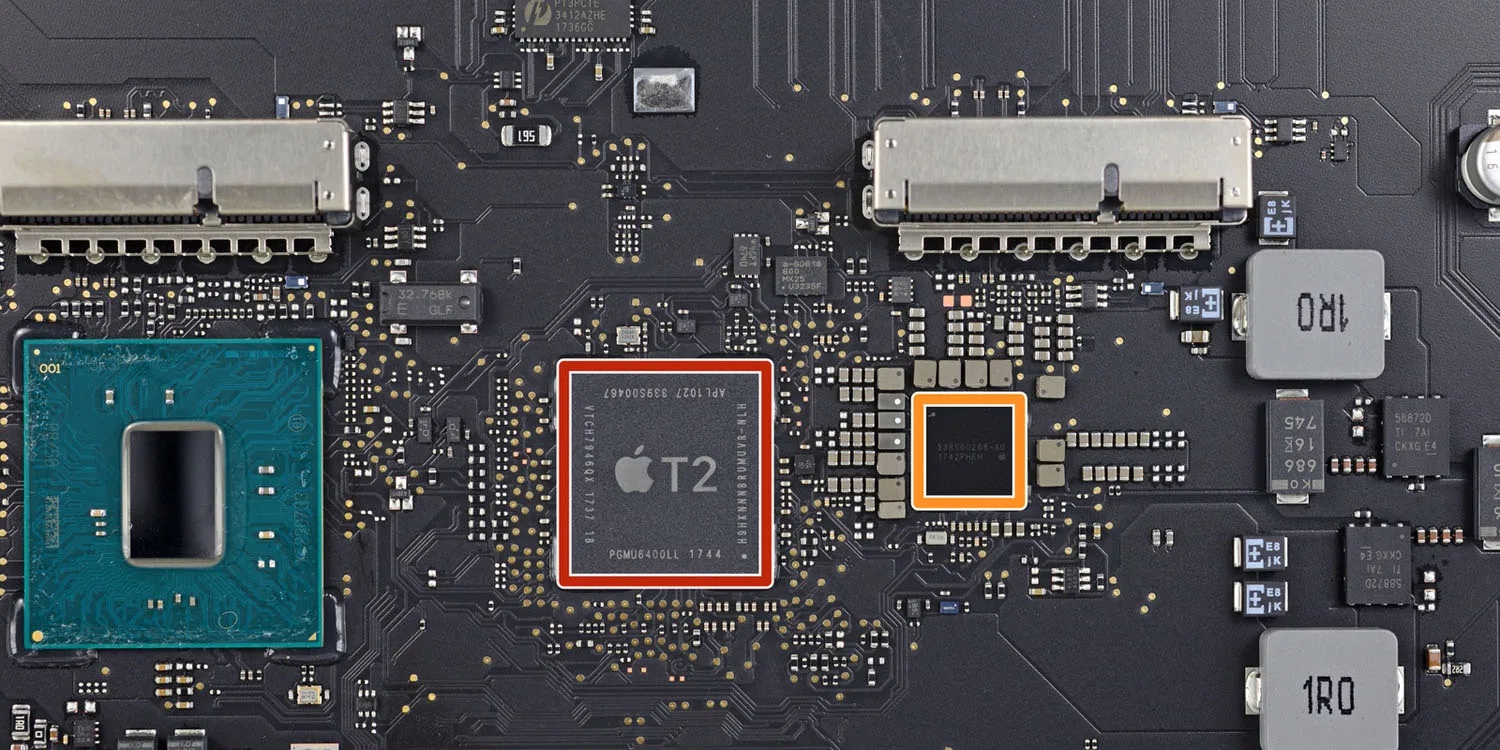
Background: The T2 chip
Apple introduced the T2 security chip in 2018, and it was used to provide a secure boot-up feature to Intel Macs from that year on.
The key to T2 security is that the chip contains both an SSD controller and a crypto engine, allowing it to instantly decrypt and encrypt data on the fly. This is similar to FileVault, but even more secure as only the T2 chip can do the decryption – and security features on the chip prevent an attacker from modifying macOS to gain access. Here’s how Apple describes the protection:
At the time that software is downloaded and prepared to install, it is personalised with a signature that includes the Exclusive Chip Identification (ECID) — a unique ID specific to the T2 chip in this case — as part of the signing request. The signature given back by the signing server is then unique and usable only by that particular T2 chip. The UEFI firmware is designed to ensure that when the Full Security policy is in effect, a given signature isn’t just signed by Apple but is signed for this specific Mac, essentially tying that version of macOS to that Mac. This helps prevent rollback attacks.
T2 Mac security vulnerability
Passware was already able to crack passwords and decrypt FileVault-protected drives on older Macs without the T2 chip. This uses GPU acceleration to achieve brute-force attacks of literally tens of thousands of passwords per second, making it a trivial task to break into these Macs.
Until recently, however, it wasn’t practical to mount brute-force attacks on Macs with a T2 chip. This is because the Mac password is not stored on the SSD, and the chip limits the number of password attempts that can be made, so you’d instead have to brute-force the decryption key, and that is so long it would take millions of years.
However, 9to5Mac has learned that Passware is now offering an add-on module that can defeat Macs with the T2 chip, apparently by bypassing the features designed to prevent multiple guesses. Having defeated this protection, users can then apply the dictionary of their choice. Passware provides a dictionary of the 550,000 most commonly-used passwords (created from various data breaches), along with a larger one of 10 billion passwords.
The process is still slower than usual, at a relatively sedate 15-ish passwords per second. In theory, this could still take thousands of years, but most people use relatively short passwords which are vulnerable to dictionary attacks. The average password length is just six characters, which can be cracked in around 10 hours.
Passware says that the add-on module is only available to government customers, as well as private companies who can supply a valid justification for its use.
What does this mean for Mac owners?
Passware requires physical access to your Mac, so is not a major concern for most of us.
If you have an older Intel Mac without a T2 chip, nothing has changed. Likewise if you own an M1 Mac. Affected machines are these:
- iMac (Retina 5K, 27-inch, 2020)
- iMac Pro
- Mac Pro (2019)
- Mac Pro (Rack, 2019)
- Mac mini (2018)
- MacBook Air (Retina, 13-inch, 2020)
- MacBook Air (Retina, 13-inch, 2019)
- MacBook Air (Retina, 13-inch, 2018)
- MacBook Pro (13-inch, 2020, Two Thunderbolt 3 ports)
- MacBook Pro (13-inch, 2020, Four Thunderbolt 3 ports)
- MacBook Pro (16-inch, 2019)
- MacBook Pro (13-inch, 2019, Two Thunderbolt 3 ports)
- MacBook Pro (15-inch, 2019)
- MacBook Pro (13-inch, 2019, Four Thunderbolt 3 ports)
- MacBook Pro (15-inch, 2018)
- MacBook Pro (13-inch, 2018, Four Thunderbolt 3 ports)
The main advice is, however, the same for everyone:
- Use long passwords – the longer, the better
- Don’t use words found in a dictionary
- Include special characters like !@$%^&*()-+=[]{}
- Only ever download apps from trusted sources
- Follow standard cybersecurity precautions
We’ve reached out to Apple for comment and will update with any response.
Photo: iFixit
FTC: We use income earning auto affiliate links. More.





Comments