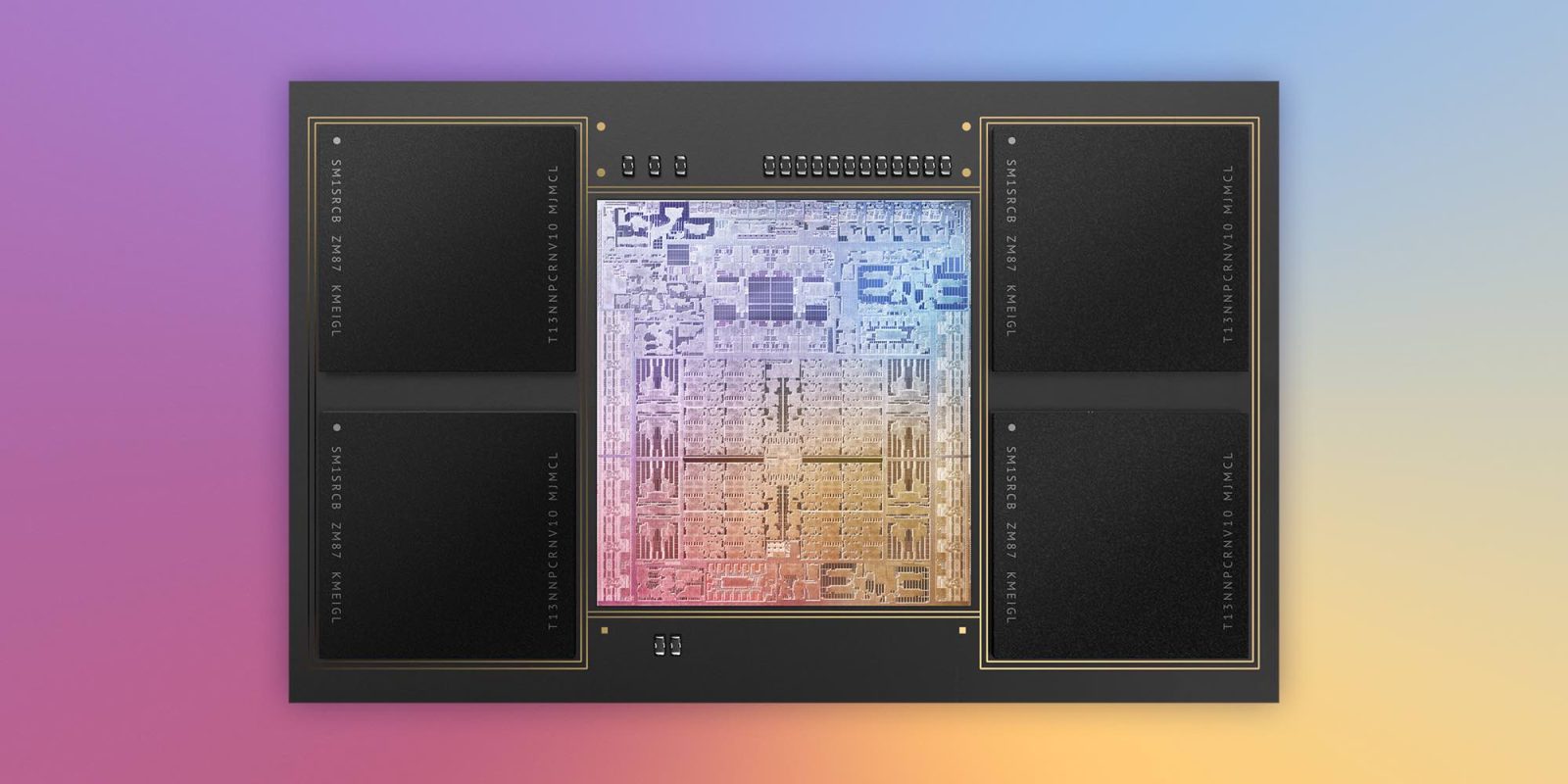
After digging into Apple Silicon, researchers have discovered a new vulnerability that affects Apple’s latest M1 and A14 chips. The Augury Apple Silicon microarchitectural flaw has been demonstrated to leak data at rest but doesn’t appear to be “that bad” at this point.
Jose Rodrigo Sanchez Vicarte at the University of Illinois at Urbana Champaign and Michael Flanders at the University of Washington led a group of researchers who published details on their discovery of the novel Augury microarchitectural Apple Silicon flaw (all details were shared with Apple prior to publishing).
The group uncovered that Apple chips use what’s called a Data-Memory Dependent Prefetcher (DMP) which looks at memory content to decide what to prefetch.
How the Augury Apple Silicon vulnerability works
Specifically, Apple’s M1, M1 Max, and A14 were tested and found to prefetch with an array-of-pointers dereferencing pattern. The researchers discovered that process can leak data that is “never read by any instruction, even speculatively!” They also believe the M1 Pro and possibly older A-series chips are vulnerable to the same flaw.
Here’s how the researchers say Apple’s DMP is different from traditional ones:
Once it has seen *arr[0] … *arr[2] occur (even speculatively!) it will begin prefetching *arr[3] onward. That is, it will first prefetch ahead the contents of arr and then dereference those contents. In contrast, a conventional prefetcher would not perform the second step/dereference operation.
As for why data at rest attacks like this are troublesome, the paper says most hardware or software defensive strategies to prevent “microarchitectural attacks assume there is some instruction that accesses the secret.” But data at rest vulnerabilities don’t work that way. Explaining further, the research says:
Any defense that relies on tracking what data is accessed by the core (speculatively or non-speculatively) cannot protect against Augury, as the leaked data is never read by the core!
But David Kohlbrenner, Assistant Professor at the University of Washington and principal investigator on the research team notes that this DMP “is about the weakest DMP an attacker can get.”
The researchers highlight that sentiment saying this vulnerability isn’t “that bad” for now and they haven’t demonstrated any “end-to-end exploits with Augury techniques at this time. Currently, only pointers can be leaked, and likely only in the sandbox threat model.”
9to5Mac’s take
This is definitely an interesting discovery and fortunately, it looks like there’s not much to worry about as the researchers see it as the “weakest DMP an attacker can get.” But of course, important discoveries like this allow Apple to make its devices more secure and get ahead of malicious use.
In the year and a half since Apple went all-in on making its own chips, we’ve only seen a few security concerns specifically around the M1 pop-up. One saw apps exchange data covertly but that wasn’t a real issue and another was custom-made Apple Silicon malware (a perennial problem on any hardware).
The researchers are not aware of Apple working on a patch for Augury, but we’ll be keeping an eye out for any developments around this flaw.
FTC: We use income earning auto affiliate links. More.






Comments