As noted by BusinessInsider, a number of security researchers and other hackers have come together to offer rewards to the first person that can “reliably and repeatedly break into an iPhone 5s” through bypassing the new TouchID fingerprint sensor feature. They aren’t looking for a software hack, however, but instead want hackers to break into the device by lifting prints, “like from a beer mug.”
It’s not exactly a legit contest, as the creators of the site are only claiming responsibility for their own bounty offers. Their bounties come out to around just $200 of the approximately $20k in pledges listed on the site.
In order to collect, you’ll have to have video proof of the process. The site’s creator explained in the “terms and conditions,” which is actually just a series of tweets:
All I ask is a video of the process from print, lift, reproduction and successful unlock with reproduced print. I’ll put money on this… Enroll print, Place it, lift it, reproduce it, use the reproduction to unlock the phone without being locked out… satisfactory video evidence of the print enrollment, lift, reproduction and successful application of the print without locking out will do.
While there’s no way of telling if most of those offering bounties will actually payout, the largest pledge comes from IOCapital for $10K:
https://twitter.com/Arturas/status/380748248589148161
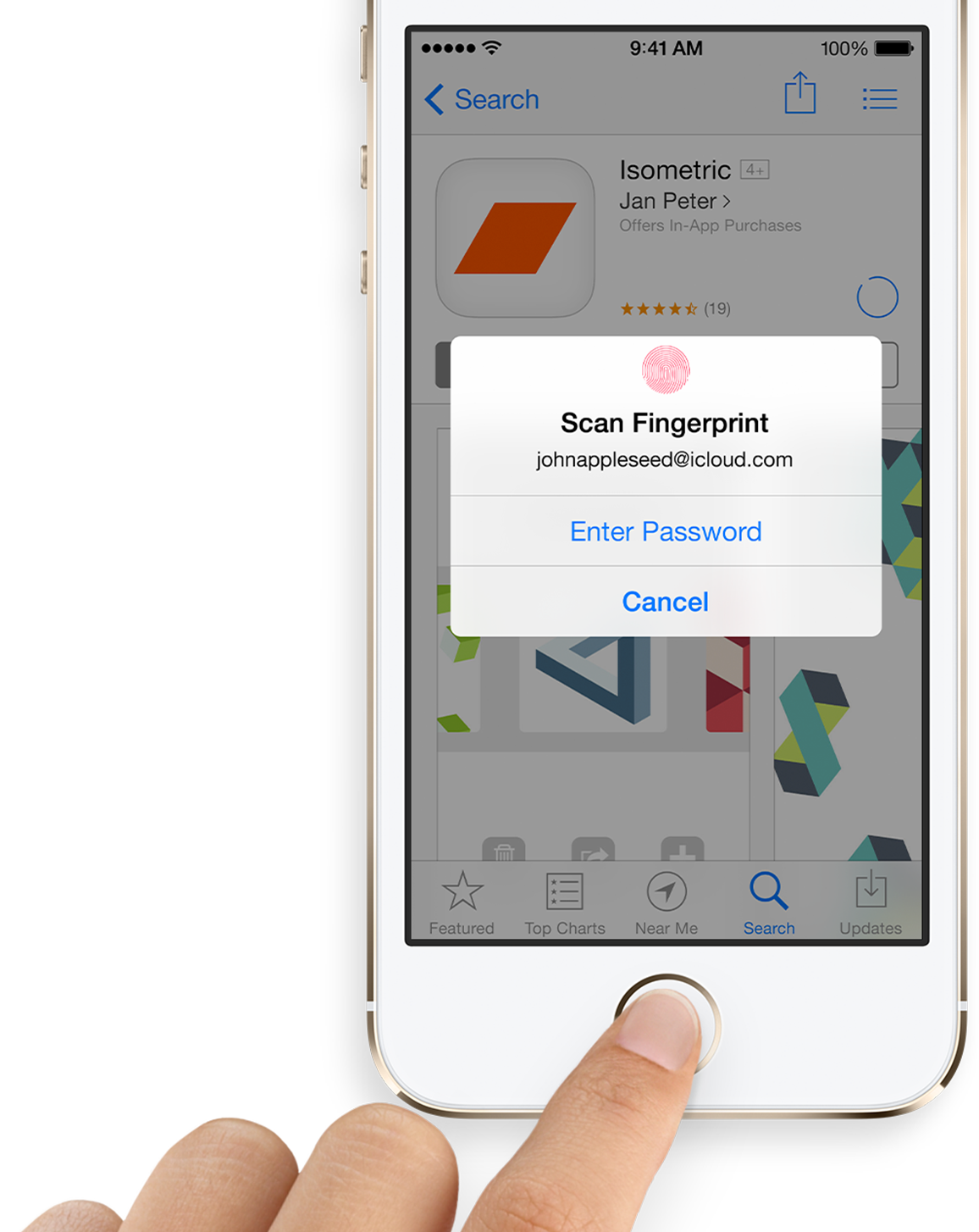
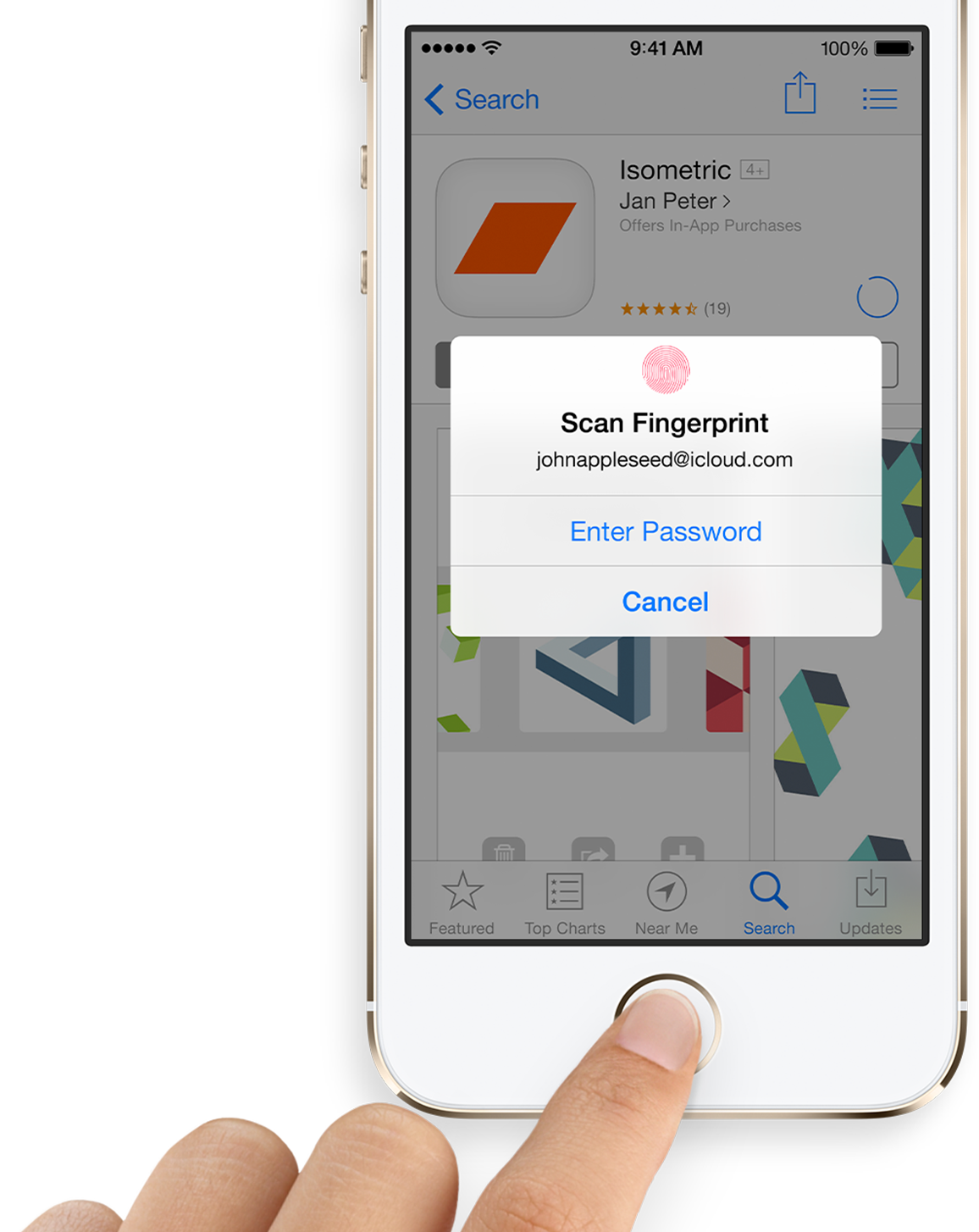
Apple said at the introduction of the iPhone 5s that “all fingerprints will be encrypted, stored securely and never uploaded to iCloud or its own servers,” but there have been a few questions surrounding how Apple’s new TouchID fingerprint sensor works. Earlier this month Apple addressed security concerns and noted some features to prevent hacking of the fingerprint sensor:
Only that passcode (not a finger) can unlock the phone if the phone is rebooted or hasn’t been unlocked for 48 hours. This feature is meant to block hackers from stalling for time as they try to find a way to circumvent the fingerprint scanner.
You can check out all of the bounties being offered and learn more through the istouchidhackedyet.com site.