9to5Toys Last Call: Beats Solo2 Headphones $90, Digits calculator for iOS free, Bluetooth audio adapter $14, more

Keep up with the best gear and deals on the web by signing up for the 9to5Toys Newsletter. Also, be sure to check us out on: Twitter, RSS Feed, Facebook, Google+ and Safari push notifications.
TODAY’S CAN’T MISS DEALS:
Last Call Updates:
Apple’s Pay Once & Play 50% off iOS game sale: Transistor, Brothers, Rules!, Implosion, Radiation Island, more
- Green Deals: Philips hue LED Starter Bundle w/ HomeKit Bridge $170, more
- Epson’s latest ‘Small-in-One’ printer weighs in at a fraction of the competition
- Twelve South introduces new TimePorter capsule for Apple Watch and charger
- Logitech Ultrathin Bluetooth Keyboard Case for iPad mini 1/2/3: $17 (Orig. $80)
- Harman Kardon Onyx Studio Wireless Bluetooth Speaker (Refurb) $60 (Orig. $400)
- Up to 50% Off select Diamondback Kids’ Bikes: Insight Hybrid $200 (Reg. $280), more
- ESPN magazine + digital Insider access 1-year subscription: $4.50 (Reg. $26+)
- Sports/Fitness: Portable Outdoor USB LED Lantern $12 (Reg. up to $18), more
- Home: Oral-B’s best selling Bluetooth Electric Toothbrush $100 (Orig. $220), more
[tweet https://twitter.com/9to5toys/status/718161248492380162 align=’center’]

Beats Solo2 Wired On-Ear Headphones (multiple colors) $90 shipped (Orig. $200), more
Digits, the calculator for humans on iOS is now available for free (Reg. $4)

Add Bluetooth to nearly any speaker w/ the Mpow Streambot Mini for $14 Prime shipped
Apple Deals:
Apple iPad Pro 12.9-inch Wi-Fi 128GB in all colors: $760 shipped (Reg. $949)
Apple 12-inch Retina MacBook 1.1GHz/8GB/256GB: $990 shipped (Reg. $1,299), more
Apple 15-inch Retina MacBook Pro (Newest Version) 2.2GHz/16GB/256GB: $1,600 shipped (Reg. $1,999)
Apple TV 4th gen: 32GB $109 (Reg. $149), 64GB $154 (Reg. $199) w/ VISA Checkout
What if I told you that you could get a great Apple Milanese Loop knockoff for a tenth of the price ($16 Prime shipped)?
Apple Watch 42mm Space Gray Milanese Loop Band + Aluminum Dock: $27 Prime shipped (Reg. $35)

Cut the Rope Time Travel for iPhone and iPad goes free for the very first time (Reg. $1)
Brothers A Tale of Two Sons iOS puzzle-adventure game gets its first price drop: $2 (Reg. $5)
Transistor action RPG for iOS matching its lowest price ever: $3 (Reg. $10)
App Store Free App of the Week: CHOMP interactive storybook goes free for the first time ($3 value)
Apple offers Day One 2 iOS journal app for free ($10 value)
MORE NEW GEAR FROM TODAY:

Audio-Technica’s best selling ATH-M50x studio headphones + FiiO A3 amp $130 shipped ($180+ value)
- Smartphone Accessories: GOOLOO Car Jump Starter Power Bank $64 (Reg. $100), more
- Daily Deals: Sony Portable Bluetooth Speaker w/ AirPlay $160, more
- LEGO Deals: Big Bang Theory Living Room $46, Minecraft Ender Dragon $49, more
- Onkyo’s 4K A/V Receiver and 5.1-Ch. Speaker bundle for $300 shipped (Reg. $400)
- Games/Apps: Assassin’s Creed Syndicate $30, iOS freebies more
- Mojang reveals 27 new skins for Minecraft Story mode, here’s how you can get them for free
- Browse reddit like a boss with a free 3-month gold membership upgrade ($12 value)
- Amazon Gold Box – Reebok running shoes 50% off: Men’s Crossfit Nano Pump Shoe $70, more
[tweet https://twitter.com/9to5toys/status/718104977198198784 align=’center’]
MORE DEALS STILL ALIVE:

iPhone SE and Galaxy S7/Edge cases in a variety of styles/colors from $3 shipped
Walmart launches iPhone SE $100 discount, other Apple/Samsung devices too!

Smartphone Accessories: Bose SoundLink Bluetooth Speaker III $249 shipped (Reg. $300), Aduro 2-Outlet USB Surge Protector $10, more
- Storage: WD My Passport Ultra 1TB USB 3.0 Portable HDD $50 (Reg. $60), more
- Learn to build amazing apps with the Apple TV Developer Course: $19 (Orig. $199)
- Buy 3 accessories, save 20%: iPad Pro Keyboard $143, Apple Pencil $87, more
- Aukey Aluminum USB-C Hubs w/ Prime shipping: 7-ports for $19 or 4-ports for $8
- Google Nexus 5X 16GB now just $230 shipped (Reg. $349)
- Discounted fans: Vornado 660 Whole Room Air Circulator $82 (Reg. $100), more
- Green Deals: 25% off Natural Magnetic Wooden Block Sets from $24, more
- Free Small Fry and Drink with the purchase of an Arby’s Sandwich!
- Grab a free Kindle download of Jane Austen’s ‘Mansfield Park’ w/ Audible Narration
- You can now live stream an MLB game every day for free courtesy of Yahoo
- Home Theater: Pioneer 4K 3D AirPlay A/V Receiver $400, more
- UE BOOM 2 Waterproof Bluetooth Speaker in all colors: $150 shipped (Reg. $200)
- T-Mobile offering $200 off any iPad when you buy an iPhone on installment plan
- Green Deals: Collapsible Solar Lantern $14, more
- Start programming with the ‘Learn Python 3.0 Visually’ Kindle eBook for $1 (Reg. $10)
- The classic-style Doom and Destiny RPG games drop to just $1 each on iOS (Reg. $3 ea)
- Game Dev Story for iOS now matching its lowest price ever: $1 (Reg. $5)
- iTunes gift cards w/ free email delivery: $100 for $90, $50 for $45, more (10% off)
- Amazon Fire TV 4K Streaming Media Player $85 (Reg. $100), more
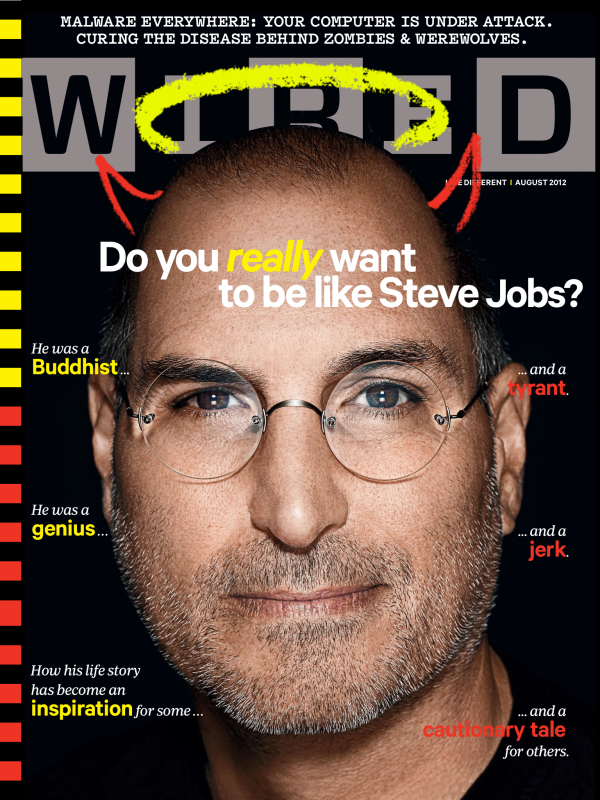
- Amazon is giving Prime members up to 3 magazine subscriptions for free: Wired, GQ, more
- Green Deals: Etekcity 3-pack of Remote Outlet Switches $17 (Reg. $25), more
- Browse the web anonymously: $60 (Orig. $80)
- Samsung 48-inch Smart UHDTVs: 3D 120Hz $925 (Reg. $1,200+), Curved 60Hz $629 (Reg. $830)
- Here’s how you can get a 90-day membership to BJ’s Warehouse for free
- Final Fantasy XV gets a new playable demo, now available for free on PS4 and Xbox One
- Green Deals: WORX WG156 2-in-1 Electric Trimmer/Edger $80 shipped (Reg. $107+), more
- Kindle First eBook freebies for April: Golden Age, The Secret Healer, Blood Defense, more
- Google Play Metal Albums for $0.99: Trivium’s Silence In The Snow (Orig. $11), more
Buy a refurbished Apple AirPort Express Wi-Fi router w/ 1-yr warranty for $49 shipped (Orig. $99)
NEW PRODUCTS & MORE:

Ryobi’s new Ultra Quiet Garage Door Opener has a Bluetooth speaker and more
- Roku introduces a new quad-core streaming stick with a slimmed down design
- Apogee releases its most affordable full-featured Mac recording interface yet
- The Yecup 365 travel mug uses your iPhone to heat or cool your drink
- ROAM-e follows you around in the sky and takes selfies on demand
- Sprint customers can now (but probably shouldn’t) pay monthly for Amazon Prime
- Seagate unveils the “world’s first” USB-powered 8TB desktop hard drive
- Sony’s new RX10 III digital camera goes big with a 24-600mm lens and 4K capabilities
- Unboxing the awesome, pricey C-3PO and Stormtrooper Bluetooth speakers [Video]
- QWERKYWRITER is a mechanical Bluetooth keyboard that takes us back to simpler times
- Build an Alexa-enabled device using a Raspberry Pi
- Review: Fitbit Alta pairs smart fitness tracking with a small and beautiful design
- The Kuvée smart wine bottle brings the Internet of Things to grapes near you
- This Kickstarter project allows up to 10 people wirelessly listen to nearly any source
- TCL’s new 4K Roku-enabled UHDTVs hit every price point
- The Tovala iOS-connected oven scans and automatically prepares your dinner


















 Facebook-owned
Facebook-owned